Businesses often search for the CERT-In auditors list when preparing for government tenders, security compliance reviews, hosting approvals, or vendor security assessments. In these situations, choosing a company that is not empanelled by CERT-In can cause delays or rejection of the security report.
This guide explains how to find the latest CERT-In empanelled auditors list for 2026, where to access the official source, and how to confirm whether an auditor is currently listed.
Steps to Find the CERT-In Empanelled Auditors List 2026
If your organization needs a security assessment from a CERT-In empanelled auditor, the first step is to access the official CERT-In empanelled auditors list pdf. This list helps businesses confirm which companies are authorized to conduct approved security audits and testing.
1. Visit the Official CERT-In Website
Start by visiting the official website of CERT-In. The organization maintains an updated list of companies that are authorized to provide information security auditing services. Accessing the list from the official source helps ensure that the information is accurate and up to date.
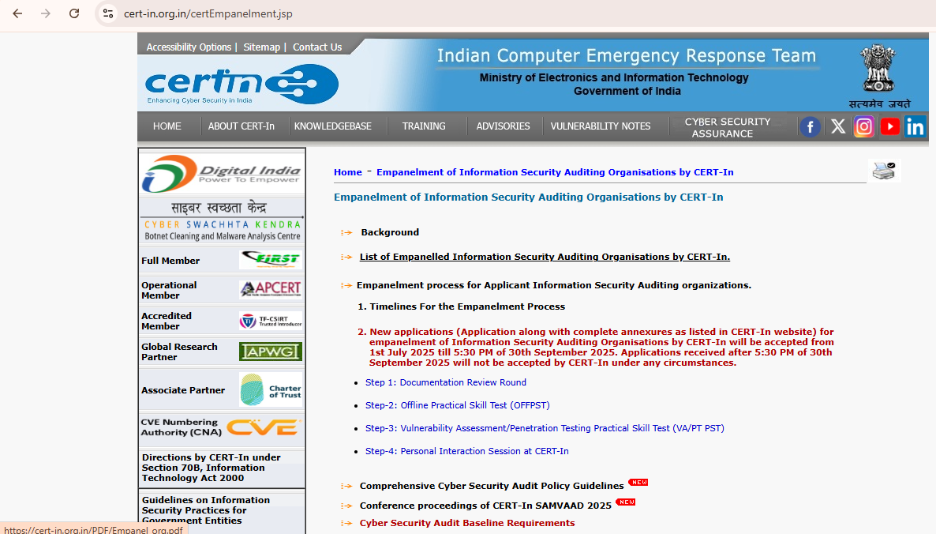
2. Locate the Empanelled Auditors Section
Once you are on the CERT-In website, navigate to the section related to Information Security Auditing Organizations or empanelled auditors. This section contains the names of companies that are approved to perform security assessments such as vulnerability assessments, penetration testing, and security audits.
3. Download the Latest Auditors List
The auditors list is regularly available as a downloadable document or a webpage containing the company details. It is provided as CERT-In empanelled companies list pdf format so organizations can easily review and share the information internally when selecting an auditor.
4. Verify the Auditor Details
Before contacting an auditor, review the details listed in the document. Check the company name, empanelment validity period, and scope of services mentioned. Verifying these details helps confirm that the company is currently empanelled and authorized to perform the required security assessment.

What Information the CERT-In Empanelled Auditors List Usually Contains?
When you download the auditors list from CERT-In, it typically provides detailed information about each empanelled security auditing organization. This information helps organizations understand the capabilities, experience, and qualifications of the auditors before selecting one for a security assessment.
1. Name of the Empanelled Organization
The document lists the official name of the company that has been approved to perform information security auditing services. It may also include the registered office address and operational location of the organization.
2. Year Since Information Security Audits Started
Many profiles mention the year the company began conducting information security audits. This helps organizations get an idea of how long the firm has been involved in security assessment activities.
3. Scope of Security Audit Capabilities
The list often includes the security audits the company can perform. These may include:
- Network security audits
- Web application security audits
- Wireless security audits
- Cloud security audits
- Compliance-related audits
- Finance sector security assessments
This section helps organizations determine whether the auditor can perform the specific type of assessment they require.
4. Audit Experience and Project Numbers
The document may also provide an overview of the number of security audits completed by the organization. In some cases, it categorizes them by sector such as government, public sector units (PSUs), or private organizations.
5. Number of Security Audits Conducted in the Last 12 Months
Some auditor profiles show the number of security audits completed within the past year. These may be categorized by audit type, such as network security audits, web application audits, compliance audits, or financial sector assessments.
6. Technical Security Team and Certifications
Another important section describes the technical team working within the organization. It may include:
- Total number of security professionals
- Security certifications held by team members
Common certifications listed may include CEH, OSCP, GIAC, ISO 27001 Lead Auditor, and other recognized information security qualifications.
7. Employee Experience and Qualifications
Certain auditor profiles provide details about individual team members, including their experience in information security, years with the organization, and security certifications.
- Name of the empanelled company
- Contact information
- Scope of empanelment
- Validity period of empanelment

Get CERT-In Security Assessment from Peneto Labs
Planning a CERT-In security assessment can involve several steps, including defining the testing scope, identifying systems that require assessment, and ensuring the report meets compliance or project requirements. Working with a professional cybersecurity firm like Peneto Labs can make this process easier and help avoid delays during audits or approvals.
Peneto Labs has been empanelled by CERT-In to conduct information security auditing services. Peneto Labs supports organizations with multiple security assessments and certificates that are commonly required by enterprises, regulators, and government platforms. These include:
- Safe-to-Host Certificate
- Web Application Security Assessment (WASA) Certificate
- API Security Assessment Certificate
- CERT-In Mobile Application VAPT Certificate
- CERT-In VAPT Audit Report
- Comprehensive VAPT Reports (Network, Thick Client etc.)
If your organization is preparing for a security assessment or compliance review, contact Peneto Labs to discuss your requirements and plan the appropriate testing for your applications, APIs, mobile platforms, or infrastructure.
Conclusion
By checking the official CERT-In empanelled auditors list published by CERT-In, businesses can confirm whether a cybersecurity firm is authorized to conduct approved security audits and VAPT assessments.
Before starting any security assessment, organizations should always verify the auditor’s empanelment status and ensure the testing scope covers their applications, networks, cloud systems, or APIs. Selecting the right CERT-In empanelled auditor like Peneto Labs helps ensure that the assessment report is preferred for compliance, government projects, and enterprise security reviews.