Mobile Application Penetration Testing
Explore the security of your business-critical iOS or Android application for vulnerabilities with Peneto Labs’ expert mobile application penetration testing
Mobile applications are developed at a speed to meet deadlines which means best practices are frequently missed. Moreover, Mobile applications often collect and store sensitive user data. This leave user data at risk both in the backend server and on the Android or IOS devices. If a hacker compromises these data it will result in a business’s reputation damage, incur large fines and possible lawsuits.
By Having Vulnerablities in your Mobile Application, you could be:

Risking Massive Data Breaches

Leaving Sensitive Client Information Exposed.
Risking Your Reputation And Your Company's

Risking Underlying Hosted Server Which May Have Critical Data.

Incur Large Fines

Risking Possible Lawsuits
It is important to secure the critical applications your company relies upon to conduct business and to store proprietary and confidential information.
How You Benefit?

Reduce The Risk Of Breaches
Our consultants specialize in simulating cybercriminals, going beyond the capabilities of automated tools and standard audits to identify complex security issues.

Satisfy Compliance Requirement
No-surprise audits: We offer thorough assessments and assistance to help you achieve compliance with relevant regulations, ensuring no unexpected compliance gaps or issues arise

Verify Your Current Security Controls
Our Comprehensive audits of your organization’s infrastructure provide factual information about the effectiveness of your current security controls

Obtain Audit Certificate
High credibility is always inherent when obtaining your audit certification from Peneto Labs. This organisation is empanelled by CERT-In to provide information Security Auditing Services.
Our Security Certifications
Our consultants hold cyber security certifications such as SANS/GIAC GXPN, GAWN, GPEN, GWAPT, GRID, GCIH, OSCE, OSWP, OSCP, CEH, CREST etc. This means your hiring WORLD CLASS SECURITY EXPERTS to fight against Hackers trying to attack your infrastructure.






How we can help you to secure your Mobile Application
Mobile Application Penetration Testing
Peneto labs offers Mobile Application penetration testing service where we simulating a real-world attack on mobile applications and platforms, with the goal to identify and exploit vulnerabilities. We work to ensure that issues are caught before they can be exploited by Hackers.

Give us an appointment
This will allow us to understand your current challenges and align us with your vision and business compliance requirements.

Let Us Assess Your Mobile Application
Our certified experts carry out high quality audits to identify security gaps including high impact risks as a result we produce comprehensive reports.

Implement our recommendations
Our well documented reports with an executable remediation plan, followed by a detailed solution walk through and Q&A sessions helps your technical team to fix issues without any difficulties.

Obtain audit certificate
Obtaining audit certificate, satisfy compliance requirements, reduce the risk of breaches and focus on your mission with peace of mind.

Give us an appointment
This will allow us to understand your current challenges and align us with your vision and business compliance requirements.

Let Us Assess Your Mobile Application
Our certified experts carry out high quality audits to identify security gaps including high impact risks as a result we produce comprehensive reports.

Implement our recommendations
Our well documented reports with an executable remediation plan, followed by a detailed solution walk through and Q&A sessions helps your technical team to fix issues without any difficulties.

Obtain audit certificate
Obtaining audit certificate, satisfy compliance requirements, reduce the risk of breaches and focus on your mission with peace of mind.
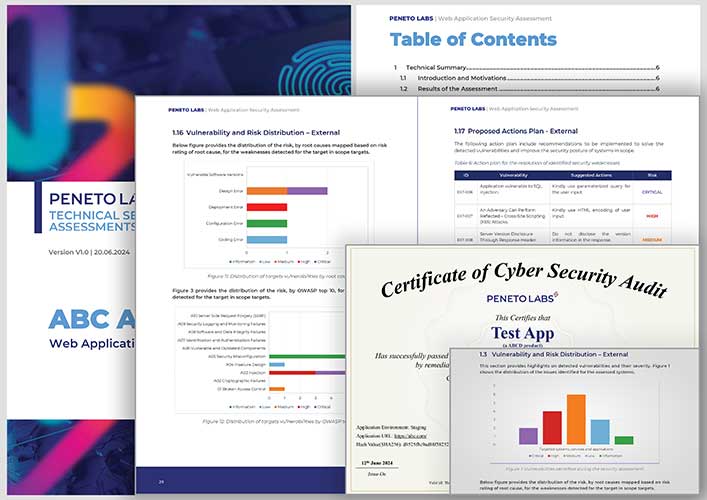
Free Sample Certificate & Penetration Testing
Report
Report
Wondering what’s include in our sample certificate and Pen test report? Take a look at our sample Pen test report and sample certificate.
Frequently Asked Questions (FAQ’s)
How Much Does Mobile Application Penetration Testing Cost?
Peneto Labs offers personalized penetration testing at transparent prices. We carefully consider tester skillset and asset complexity to provide accurate quotes, ensuring comprehensive security assessments for your digital assets. The time required for testing may vary based on the application’s size and complexity. We aim for flexible pricing, accommodating different project sizes for fair and precise cost assessments. Our pricing model is variable and considers factors like the number of IP addresses, retesting needs and required expertise.
What Is The Difference Between A Vulnerability Scan, Vulnerability Assessment, And A Penetration Test?
Clarification is essential: A vulnerability scan, vulnerability assessment, or automated scan cannot be considered a penetration testing.
While a vulnerability scan utilizes automated tools to detect known weaknesses, a vulnerability assessment involves a more comprehensive evaluation, manually inspecting and assessing the severity of vulnerabilities. On the other hand, a true penetration test simulates real-world attacks to identify and exploit security vulnerabilities, demonstrating the potential risks associated with those vulnerabilities. Trust our experienced team to provide specialized vulnerability assessments and penetration testing services, delivering comprehensive insights and solutions to bolster your organization’s security. Contact us today to schedule a reliable and thorough assessment tailored to your specific needs.
Consult Our Experts
WhatsApp us